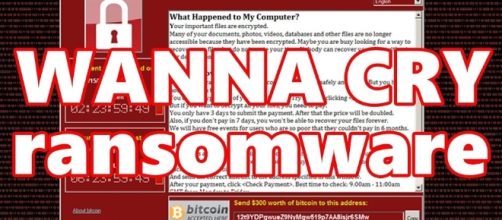
It is not hard to believe the report by Symantec Corp. and Kaspersky Lab that technical evidence indicates a North Korean hacking group is behind the WannaCry Ransomware attack last week. The basis of their suspicion is that some of the codes in an older version of the malware were used before by the Pyongyang-based Lazarus Group.
Elite group of North Korean hackers
Simon Choi, a senior researcher at Huari Labs, a South Korean cybersecurity company, confirmed that WannaCry ransomware’s codes were similar to the backdoor malicious codes of North Korea.
Hacking, after all, is a daily activity in North Korea, as a group made up of 6,800 state hackers extort and undermine people, enterprises, and governments across nations, as Time reported.
The Korea Institute of Liberal Democracy based in Seoul estimated that members of the elite squad of North Korea who are into fraud, blackmail, and online gamblin, earn yearly about $860 million. Their day-to-day operations are focused on earning foreign currency via cybercrimes as Lim Jong-in, a professor at the Department of Cyber Defense at Korea University, said.
A threat to national security
The operations of the North Korean hacking group, whose cyber security experts observed have hacking skills on par with the U.S., China, Russia, and Israel, could become a global headache.
Lim Jong-in said that would occur when Pyongyang’s cybercrimes morph into offensive Cyber attacks during times of war and crisis. He said the threat would keep on advancing as attacks on national infrastructure become a serious national security threat.
North Korea has a history of cyber attacks such as in 2014 when it hit Sony Entertainment for producing the film “The Interview.” The satire movie lampooned the family of Kim Jong-un, the country’s leader.
Pyongyang’s first was a decade earlier after the collapse of a six-party denuclearization discussions.
North Korea launched Distributed Denial of Service attacks that targeted Seoul and U.S. government departments, media, and financial portals by using malware that wipes disks. In 2011, North Korea attacked South Korea and the U.S.
military again using the “10 Days of Rain” of the McAfee antivirus company. It jammed the GPS system of hundreds of civilian vessels and aircrafts. In May 2013, the group hacked financial institutions in South Korea and its Domain Name System registry.
Technology Review reported that besides WannaCry, there is another malware, Adylkuzz, which has been infecting insecure Windows devices. It installs a software, seizes the computer’s data and then asks for payment of a ransom using Monero, another cryptocurrency.